ISC CISSP exam ready here! Get the latest CISSP exam exercise questions and exam dumps pdf for free! 100% pass the exam to select
the full ISC CISSP exam dumps the link to get VCE or PDF. All exam questions are updated!
leads4pass offers the latest ISC CISSP Google Drive
[Latest updates] Free ISC CISSP dumps pdf download from Google Drive: https://drive.google.com/file/d/1ZDfJ0oEGB5f0dIUOcW4AYAbkQBO4ayQa/
Buklsainsa Exam Table of Contents:
- ISC CISSP Practice testing questions from Youtube
- latest updated ISC CISSP exam questions and answers
- leads4pass ISC discount code 2021
- About leads4pass
ISC CISSP Practice testing questions from Youtube
latest updated ISC CISSP exam questions and answers
QUESTION 1
An organization has discovered that users are visiting unauthorized websites using anonymous proxies.
Which of the following is the BEST way to prevent future occurrences?
A. Remove the anonymity from the proxy
B. Analyze Internet Protocol (IP) traffic for proxy requests
C. Disable the proxy server on the firewall
D. Block the Internet Protocol (IP) address of known anonymous proxies
Correct Answer: C
QUESTION 2
In order to assure authenticity, which of the following are required?
A. Confidentiality and authentication
B. Confidentiality and integrity
C. Authentication and non-repudiation
D. Integrity and non-repudiation
Correct Answer: D
QUESTION 3
With what frequency should monitoring of a control occur when implementing Information Security Continuous
Monitoring (ISCM) solutions?
A. Continuously without exception for all security controls
B. Before and after each change of the control
C. At a rate concurrent with the volatility of the security control
D. Only during system implementation and decommissioning
Correct Answer: B
QUESTION 4
In the Software Development Life Cycle (SDLC), maintaining accurate hardware and software inventories is a critical
part of
A. systems integration.
B. risk management.
C. quality assurance.
D. change management.
Correct Answer: D
QUESTION 5
Which of the following types of technologies would be the MOST cost-effective method to provide a reactive control for
protecting personnel in public areas?
A. Install mantraps at the building entrances
B. Enclose the personnel entry area with polycarbonate plastic
C. Supply a duress alarm for personnel exposed to the public
D. Hire a guard to protect the public area
Correct Answer: D
QUESTION 6
Which of the following is the MOST efficient mechanism to account for all staff during a speedy nonemergency
evacuation from a large security facility?
A. Large mantrap where groups of individuals leaving are identified using facial recognition technology
B. Radio Frequency Identification (RFID) sensors worn by each employee scanned by sensors at each exitdoor
C. Emergency exits with push bars with coordinates at each exit checking off the individual against a predefined list
D. Card-activated turnstile where individuals are validated upon exit
Correct Answer: B
QUESTION 7
Which of the following is the MOST important output from a mobile application threat modeling exercise according to
Open Web Application Security Project (OWASP)?
A. Application interface entry and endpoints
B. The likelihood and impact of a vulnerability
C. Countermeasures and mitigations for vulnerabilities
D. A data flow diagram for the application and attack surface analysis
Correct Answer: D
QUESTION 8
Additional padding may be added to toe Encapsulating Security Protocol (ESP) b trailer to provide which of the
following?
A. Access control
B. Partial traffic flow confidentiality
C. Protection against replay attack
D. Data origin authentication
Correct Answer: C
QUESTION 9
Information security metrics provide the GREATEST value tp management when based upon the security manager\\’s
knowledge of which of the following?
A. Likelihood of a security breach
B. Value of information assets
C. Cost of implementing effective controls
D. Benefits related to quantitative analysts
Correct Answer: B
QUESTION 10
Which programming methodology allows a programmer to use pre-determined blocks of code end consequently
reducing development time and programming costs?
A. Application security
B. Object oriented
C. Blocked algorithm
D. Assembly language
Correct Answer: B
QUESTION 11
Which of the following is the BEST way to verify the integrity of a software patch?
A. Cryptographic checksums
B. Version numbering
C. Automatic updates
D. Vendor assurance
Correct Answer: A
QUESTION 12
The World Trade Organization\\’s (WTO) agreement on Trade-Related Aspects of Intellectual Property Rights (TRIPS)
requires authors of computer software to be given the
A. right to refuse or permit commercial rentals.
B. right to disguise the software\\’s geographic origin.
C. ability to tailor security parameters based on location.
D. ability to confirm license authenticity of their works.
Correct Answer: A
QUESTION 13
When transmitting information over public networks, the decision to encrypt it should be based on
A. the estimated monetary value of the information.
B. whether there are transient nodes relaying the transmission.
C. the level of confidentiality of the information.
D. the volume of the information.
Correct Answer: C
leads4pass ISC discount code 2021
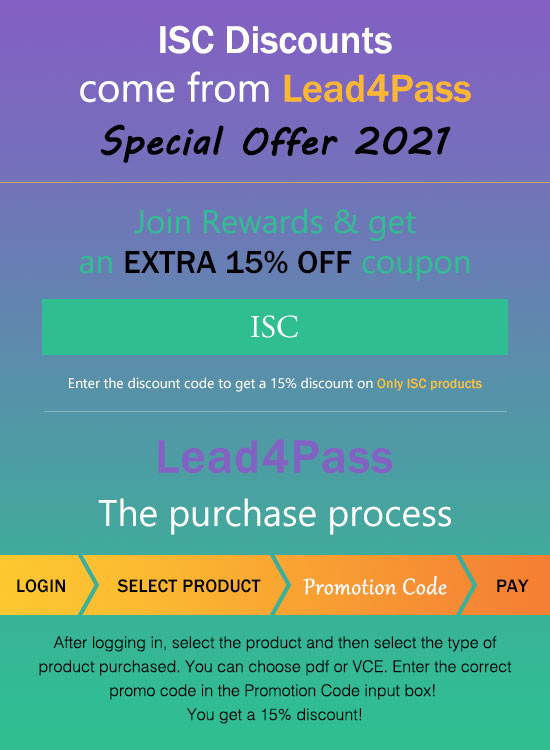
leads4pass shares the latest ISC exam discount code “ISC“. Enter the discount code to get a 15% discount!
About leads4pass
leads4pass has 8 years of exam experience! A number of professional ISC exam experts! Update exam questions throughout the year! The most complete exam questions and answers! The safest buying experience! The greatest free sharing of exam practice questions and answers!
Our goal is to help more people pass the ISC exam! Exams are a part of life, but they are important!
In the study, you need to sum up the study! Trust leads4pass to help you pass the exam 100%!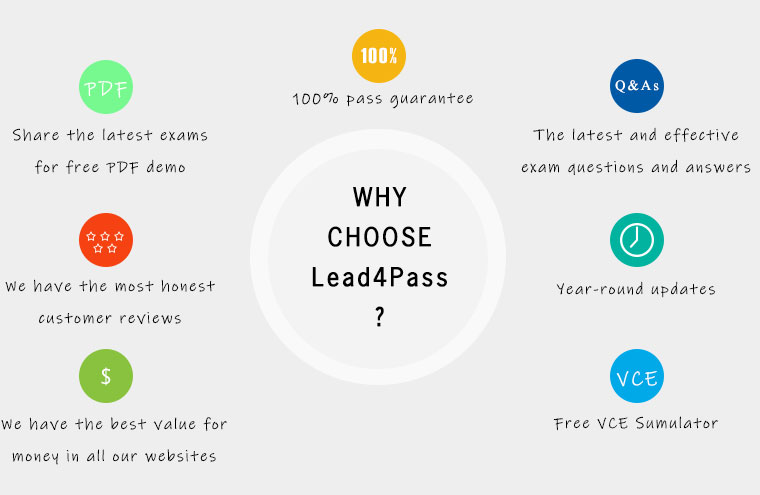
Summarize:
Buklsainsa free to share ISC CISSP exam exercise questions, CISSP pdf, CISSP exam video! leads4pass updated exam questions and answers throughout the year!
Make sure you pass the exam successfully. Select lead4Pass CISSP to pass the ISC CISSP exam “Certified Information Systems Security Professional“.
ps.
Latest update leads4pass CISSP exam dumps: https://www.leads4pass.com/cissp.html (970 Q&As)
[Latest updates] Free ISC CISSP Dumps pdf download from Google Drive: https://drive.google.com/file/d/1ZDfJ0oEGB5f0dIUOcW4AYAbkQBO4ayQa/