EC-COUNCIL 312-50V11 exam dumps have been updated, all exam questions and answers are verified!
Guaranteed to be true and valid. Get the complete EC-COUNCIL 312-50V11 exam dumps https://www.leads4pass.com/312-50v11.html. To help you successfully pass the first exam. You can take part in the EC-COUNCIL 312-50V11 free exam questions online practice test on this site to verify your strength.
This site shares all types of IT certification exam questions, including Cisco, Microsoft, CompTIA, Avaya, IBM, Amazon, EC-COUNCIL, etc. If you want a complete series of EC-COUNCIL free practice questions blog, you can visit latestvce.com.
EC-COUNCIL 312-50V11 exam PDF free online download
Google Drive: https://drive.google.com/file/d/10VAQob2giQ-xeTwFx-xjMXI9wBiCctuA/view?usp=sharing
[2022 Updated]:https://drive.google.com/file/d/1IW-vsqqsN4-yp3ZoNmhIm42BJE6y58_m/
[2022 Updated] dumps exam material
QUESTION 1:
“……..is an attack-type for a rogue Wi-Fi access point that appears to be a legitimate one offered on the premises, but actually has been set up to eavesdrop on wireless communications. It is the wireless version of the phishing scam. An attacker fools wireless users into connecting a laptop or mobile phone to a tainted hot spot by posing as a legitimate provider. This type of attack may be used to steal the passwords of unsuspecting users by either snooping the communication link or by phishing, which involves setting up a fraudulent website and luring people there.”
Fill in the blank with the appropriate choice.
A. Evil Twin Attack
B. Sinkhole Attack
C. Collision Attack
D. Signal Jamming Attack
Correct Answer: A
QUESTION 2:
How can rainbow tables be defeated?
A. Use of non-dictionary words
B. All uppercase character passwords
C. Password salting
D. Lockout accounts under brute force password cracking attempts
Correct Answer: C
QUESTION 3:
You want to analyze packets on your wireless network. Which program would you use?
A. Wireshark with Airpcap
B. Airsnort with Airpcap
C. Wireshark with Winpcap
D. Ethereal with Winpcap
Correct Answer: A
QUESTION 4:
Nicolas just found a vulnerability on a public-facing system that is considered a zero-day vulnerability. He sent an email to the owner of the public system describing the problem and how the owner can protect themselves from that vulnerability. He also sent an email to Microsoft informing them of the problem that their systems are exposed to. What type of hacker is Nicolas?
A. Red hat
B. white hat
C. Black hat
D. Gray hat
Correct Answer: B
QUESTION 5:
Ron, a security professional, was pen testing web applications and SaaS platforms used by his company. While testing, he found a vulnerability that allows hackers to gain unauthorized access to API objects and perform actions such as view, updating, and delete sensitive data of the company. What is the API vulnerability revealed in the above scenario?
A. Code injections
B. Improper use of CORS
C. No ABAC validation
D. Business logic flaws
Correct Answer: B
It is highly recommended that you participate in this [2022 Updated] complete 312-50V11 online practice, click here for more exam questions and answers
Next, you can take the EC-COUNCIL 312-50V11 exam practice test first
The answer is announced at the end of the article
QUESTION 1
If a tester is attempting to ping a target that exists but receives no response or a response that states the destination is
unreachable, ICMP may be disabled and the network may be using TCP. Which other option could the tester use to get
a response from a host using TCP?
A. Traceroute
B. Hping
C. TCP ping
D. Broadcast ping
QUESTION 2
Which method of password cracking takes the most time and effort?
A. Dictionary attack
B. Shoulder surfing
C. Rainbow tables
D. Brute force
QUESTION 3
The following is an entry captured by a network IDS. You are assigned the task of analyzing this entry. You notice the
value 0x90, which is the most common NOOP instruction for the Intel processor. You figure that the attacker is
attempting a buffer overflow attack.
You also notice “/bin/sh” in the ASCII part of the output.
As an analyst what would you conclude about the attack?
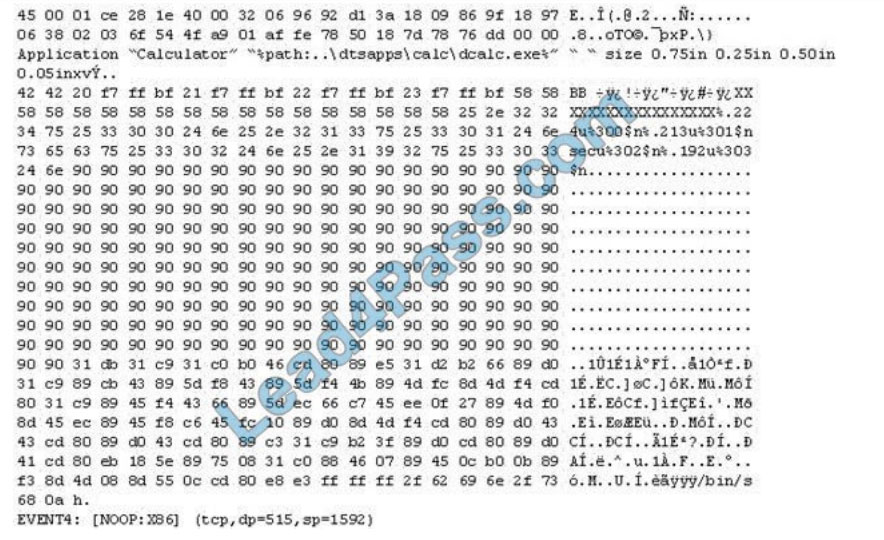
A. The buffer overflow attack has been neutralized by the IDS
B. The attacker is creating a directory on the compromised machine
C. The attacker is attempting a buffer overflow attack and has succeeded
D. The attacker is attempting an exploit that launches a command-line shell
QUESTION 4
Joseph was the Web site administrator for Mason Insurance in New York, who\’s main Web site was located at
www.masonins.com. Joseph uses his laptop computer regularly to administer the Web site. One night, Joseph received
an urgent phone call from his friend, Smith. According to Smith, the main Mason Insurance website had been
vandalized! All of its normal content was removed and replaced with an attacker\’s message \’\’ Hacker Message: You
are dead! Freaks!” From his office, which was directly connected to Mason Insurance\’s internal network, Joseph surfed
to the Web site using his laptop. In his browser, the Web site looked completely intact.
No changes were apparent. Joseph called a friend of his at his home to help troubleshoot the problem. The Web site
appeared defaced when his friend visited using his DSL connection. So, while Smith and his friend could see the
defaced page, Joseph saw the intact Mason Insurance website. To help make sense of this problem, Joseph decided
to access the Web site using his dial-up ISP. He disconnected his laptop from the corporate internal network and used
his modem to dial up the same ISP used by Smith. After his modem connected, he quickly typed www.masonins.com in
his browser to reveal the following web page:

After seeing the defaced Web site, he disconnected his dial-up line, reconnected to the internal network, and used
Secure Shell (SSH) to log in directly to the Web server. He ran Tripwire against the entire Web site and determined that
every system file and all the Web content on the server were intact. How did the attacker accomplish this hack?
A. ARP spoofing
B. SQL injection
C. DNS poisoning
D. Routing table injection
QUESTION 5
Alice, a professional hacker, targeted an organization\’s cloud services. She infiltrated the target MSP provider by
sending spear-phishing emails and distributed custom-made malware to compromise user accounts and gain remote
access to the cloud service. Further, she accessed the target customer profiles with her MSP account, compressed the
customer data, and stored them in the MSP. Then, she used this information to launch further attacks on the target
organization. Which of the following cloud attacks did Alice perform in the above scenario?
A. Cloud hopper attack
B. Cloud cryptojacking
C. Cloudborne attack
D. Man-in-the-cloud (MITC) attack
Explanation: Operation Cloud Hopper was an in-depth attack and theft of data in 2017 directed at MSP within the UK
(U.K.), us (U.S.), Japan, Canada, Brazil, France, Switzerland, Norway, Finland, Sweden, South Africa, India, Thailand,
South Korea and Australia. The group used MSP as intermediaries to accumulate assets and trade secrets from MSP
client engineering, MSP industrial manufacturing, retail, energy, pharmaceuticals, telecommunications, and government agencies.Operation Cloud Hopper used over 70 variants of backdoors, malware, and trojans. These were delivered through spear-phishing emails. The attacks scheduled tasks or leveraged services/utilities to continue Microsoft Windows systems albeit the pc system was rebooted. It installed malware and hacking tools to access systems and steal data.
QUESTION 6
Which command can be used to show the current TCP/IP connections?
A. Netsh
B. Netstat
C. Net use connection
D. Net use
QUESTION 7
In this attack, a victim receives an e-mail claiming from PayPal stating that their account has been disabled and
confirmation is required before activation. The attackers then scam to collect not one but two credit card numbers, ATM PIN numbers, and other personal details. Ignorant users usually fall prey to this scam.
Which of the following statement is incorrect related to this attack?
A. Do not reply to email messages or popup ads asking for personal or financial information
B. Do not trust telephone numbers in e-mails or popup ads
C. Review credit card and bank account statements regularly
D. Antivirus, anti-spyware, and firewall software can very easily detect these types of attacks
E. Do not send credit card numbers, and personal or financial information via e-mail
QUESTION 8
A company\’s Web development team has become aware of a certain type of security vulnerability in their Web
software. To mitigate the possibility of this vulnerability being exploited, the team wants to modify the software
requirements to disallow users from entering HTML as input into their Web application.
What kind of Web application vulnerability likely exists in their software?
A. Cross-site scripting vulnerability
B. SQL injection vulnerability
C. Web site defacement vulnerability
D. Gross-site Request Forgery vulnerability
QUESTION 9
Dorian Is sending a digitally signed email to Polly, with which key is Dorian signing this message and how is Poly
validating It?
A. Dorian is signing the message with his public key. and Poly will verify that the message came from Dorian by using
Dorian\’s private key.
B. Dorian Is signing the message with Poly’s public key. and Poly will verify that the message came from Dorian by using Dorian\’s public key.
C. Dorian is signing the message with his private key. and Poly will verify that the message came from Dorian by using
Dorian\’s public key.
D. Dorian is signing the message with Poly’s private key. and Poly will verify mat the message came from Dorian by
using Dorian\’s public key.
QUESTION 10
What is the way to decide how a packet will move from an untrusted outside host to a protected inside that is behind a
firewall, which permits the hacker to determine which ports are open and if the packets can pass through the packet-filtering of the firewall?
A. Session hijacking
B. Firewalking
C. Man-in-the-middle attack
D. Network sniffing
QUESTION 11
Take a look at the following attack on a Web Server using obstructed URL:
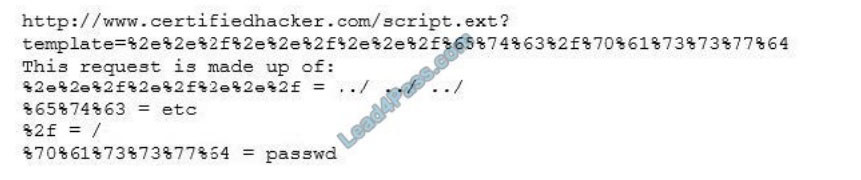
How would you protect from these attacks?
A. Configure the Web Server to deny requests involving “hex-encoded” characters
B. Create rules in IDS to alert on strange Unicode requests
C. Use SSL authentication on Web Servers
D. Enable Active Scripts Detection at the firewall and routers
QUESTION 12
Log monitoring tools performing behavioral analysis have alerted several suspicious logins on a Linux server occurring
during non-business hours. After further examination of all login activities, it is noticed that none of the logins have
occurred during typical work hours. A Linux administrator who is investigating this problem realizes the system time on
the Linux server is wrong by more than twelve hours. What protocol used on Linux servers to synchronize the time has
stopped working?
A. Time Keeper
B. NTP
C. PPP
D. OSPP
QUESTION 13
Which of the following allows attackers to draw a map or outline the target organization\’s network infrastructure to
know about the actual environment that they are going to hack?
A. Vulnerability analysis
B. Malware analysis
C. Scanning networks
D. Enumeration
Publish the answer
| Q1 | Q2 | Q3 | Q4 | Q5 | Q6 | Q7 | Q8 | Q9 | Q10 | Q11 | Q12 | Q13 |
| B | D | D | C | A | A | D | A | C | B | B | B | C |
EC-COUNCIL 312-50V11 exam PDF free online download
Google Drive: https://drive.google.com/file/d/10VAQob2giQ-xeTwFx-xjMXI9wBiCctuA/view?usp=sharing
[2022 Updated]: https://drive.google.com/file/d/1IW-vsqqsN4-yp3ZoNmhIm42BJE6y58_m/
The free EC-COUNCIL 312-50V11 content shared on this site is the latest update in November and is part of the leads4pass 312-50V11 dumps. Complete dumps of 312-50V11 https://www.leads4pass.com/312-50v11.html (Total Questions: 528 Q&A). Help you successfully pass the exam.
Finally, thanks for reading! Like to collect and share!
PS. More related EC-COUNCIL free exam questions -> latestvce.com